SimpleIoTDecoy™
A Deceptive Honeypot for Intrusion Detection
Overview
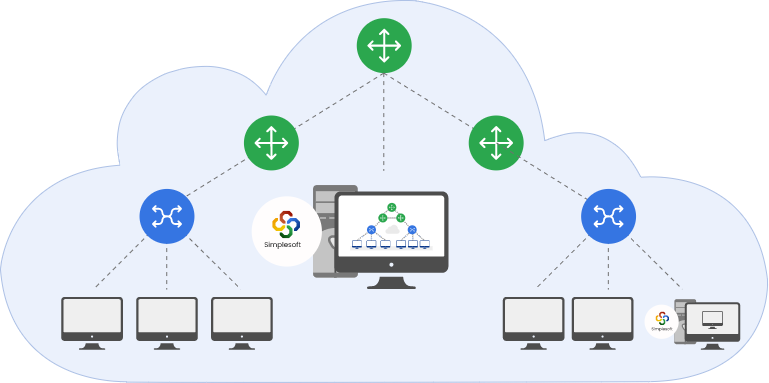
SimpleIoTDecoy supports many of the common IoT and network management protocols like MQTT, CoAP, Modbus, BACnet, HTTP/s, SNMP, Telnet, SSH, IPMI, TL1, Netconf and even LoRa. The Decoy can “learn” from existing devices to duplicate them and then run inside your intranet on computers/VMs using unused IPs to create a mixture of real and decoy devices.
SimpleIoTDecoy supports many of the common IoT and network management protocols like MQTT, CoAP, Modbus, BACnet, HTTP/s, SNMP, Telnet, SSH, IPMI, TL1, Netconf and even LoRa. The Decoy can “learn” from existing devices to duplicate them and then run inside your intranet on computers/VMs using unused IPs to create a mixture of real and decoy devices.
SimpleIoTDecoy, using patented technology, will then simply listen for incoming requests and respond to them appropriately based on the learnt data and log the interaction. It will also flag intrusions when it receives requests from unknown entities or receives requests that are different from ones it has received before from known entities. White lists of known entities and requests get automatically populated by accepting requests during a specified interval or created manually. Request fingerprinting is used to distinguish between similar requests sent from known entities that have been compromised.
Both IPv4 and IPv6 protocols are supported and SimpleIoTDecoy can run on physical as well as virtual machines.
Benefits
- The SimpleIoTDecoy adds one more security tool to an IT department’s arsenal for intrusion detection within the intranet. When hackers infiltrate the intranet, they typically scan the network to discover the devices connected to it.
- SimpleIoTDecoy device will show up alongside real devices in the scan and appear just as real. The Decoy will respond back to queries like a real device keeping the intruder engaged, while silently keeping a log of the requests made and raising an alarm to identify compromized servers used to send the requests.
- The logs can be used to run forensics to analyze the mode of operation of the intruders without putting real resources at risk. Intrusion alerts can be forwarded to the main NMS in the form of SNMP traps and syslog messages. The logs can also be used to train machine learning algorithms for future intrusion detection.

Operation
Only a few simple steps are required to start using the SimpleIoTDecoy. They are:
- Use the built-in learner utilities to record packet exchanges from real devices.
- Use this learnt data as a template to create decoys and assign them unused IPs on your intranet.
- Wait for SimpleIoTDecoy to detect intrusions and send alerts. Examine logs to run forensics.
Availability
Please email sales@simplesoft.com for limited trials.
System Requirements
- 64-bit Linux OS.
SimpleIoTSimulator Overview
This short tutorial will give you an overview on SimpleSoft’s IoT Management Simulators which can be used to simulate thousands of gateways and sensors.

SimpleSoft - an Industry Leader
Resources
- Video
- Product Updates
- Blogs
- White Paper
SimpleSoft Network Simulator Overview
SimpleSoft Agent Tester Overview
SimpleSoft SimpleIoTSimulator Overview
SimpleSoft releases Version 27.5 of SimpleAgentPro/Enterprise
SimpleAgentPro/Enterprise 27.5 now GetBulk based, faster learning, include file support in Telnet modeling files to reduce duplication, automatic handling of filters in Cisco IOS CLI commands,…
Release Notes
December 20, 2023
SimpleSoft releases Version 27.0 of SimpleAgentPro/Enterprise
SimpleAgentPro/Enterprise 27.0 now supports common data representation of variables for use by many management protocols, saving of configuration command information during CLI provisioning, simplified GPB buffer specification for Telemetry, Modeling file debugger,…
Release Notes
June 29, 2023
SimpleSoft releases Version 26.5 of SimpleAgentPro/Enterprise
SimpleAgentPro/Enterprise 26.5 now supports performance statistics in Netconf, provides remote host/port information in Telnet/SSH for filtering, allows timer_action to be staggered in SNMP,…
Release Notes
December 20, 2022
SimpleSoft releases Version 26.0 of SimpleAgentPro/Enterprise
SimpleAgentPro/Enterprise 26.0 now enhances Telemetry support in HTTP2/client and HTTP2, adds valuelist support in Netconf data modeling, AES-192-C and AES-256-C support for Cisco key initialization in SNMP,…
Release Notes
July 29, 2022
SimpleSoft releases Version 25.5 of SimpleAgentPro/Enterprise
SimpleAgentPro/Enterprise 25.5 now adds enhanced Netconf support for data modeling and namespaces, improved Telnet config command score handling, HTTP/2 server response generation without data,…
Release Notes
December 14, 2021
SimpleSoft releases Version 25.0 of SimpleAgentPro/Enterprise
SimpleAgentPro/Enterprise 25.0 now includes support for HTTP/2 client for dial-out telemetry with gRPC, exporting and importing of maps, device diagnostic connectivity checking, support for a config command score to give different show command responses after config changes in Telnet/SSH,…
Release Notes
July 27, 2021